‘00000000’ – Minuteman intercontinental ballistic missile launch code
Alarmingly at one time, the U.S. had no secret launch codes on its nuclear missiles at all. Then in 1962, the White House had them installed in an attempt to bring some sense of security. Despite the strong objections of the U.S. Strategic Air Command who bemoaned that the extra protection may affect deployability speeds, the codes became a reality. However, to effectively circumvent the White House directive, the “secret unlock codes” were set to eight zeros.Bruce Blair, a former Minuteman missile launch control officer, noted that “the locks had been installed… but everyone knew them.”
How is this relevant? Well, it resembles what effectively takes place in many businesses today. The upper levels of an organisation attempting to implement more stringent security procedures to safeguard itself and its information better. While employees tend to resist as they fear it may impact productivity.
It is clear that both concerns are legitimate and have to be taken into consideration if a working balance between safety and productivity is to be adopted.
What the figures say
A 2019 study commissioned by the National Cyber Security Centre has revealed several concerning statistics surrounding password practices:
- 30% of people do not always use a password for smartphones or tablets.
- 45% do not always use a strong, separate password for their main email account.
- 91% admitted they use the same password across multiple online accounts.
- 92% do not change passwords regularly.
- 98% do not use Multi-Factor Authentication.
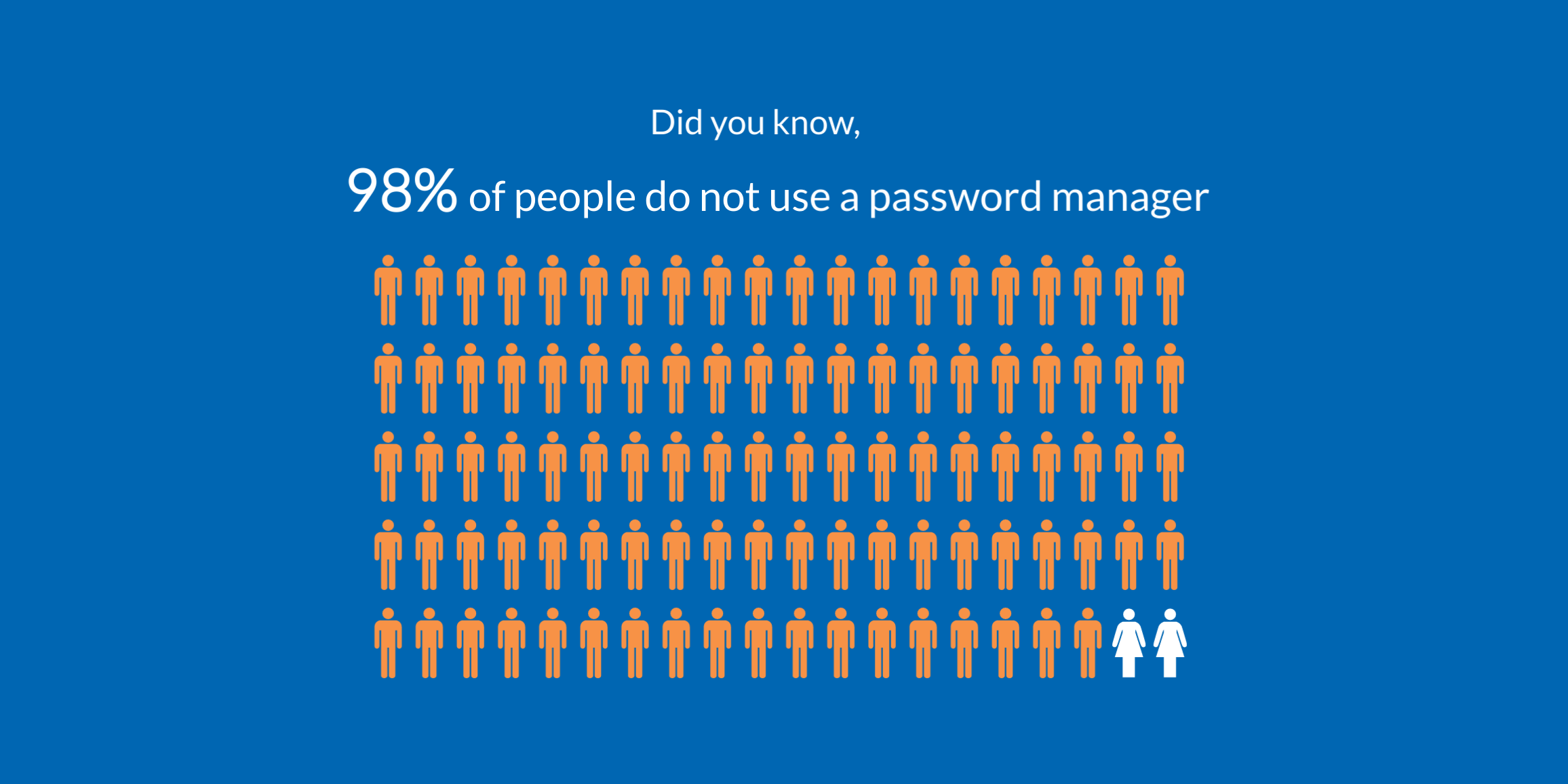
- 98% do not use a password manager.
- 97% write down passwords.
While concerning breaches, in which password compromise often plays a significant role; it was found by the Verizon 2019 Data Breach Investigations Report, that 43% of data breach victims are categorised as small businesses. This is highly problematic, given small businesses are generally the least equipped to deal with and survive such attacks.
Despite the level of damage done by such attacks, the level of sophistication and methods used aren’t as high-tech as you may believe. Let's take a look at the three overarching ways personal credentials become manipulated so you can defend against them.
How it happens
Phishing – When a hacker sends an email or another form of correspondence requesting personal details, disguised as an urgent request such as ‘change of password required immediately.’ Unfortunately, many people fall prey to this tactic, which is designed to look and feel as legitimate as possible.
Reusing Credentials – This method involves the reuse of stolen credentials from one application and applying them to another. The 2018 LastPass Global Password Security Report found that 50% of people do not create different passwords for personal and work accounts. If a hacker has either managed to purchase your password online or steal it from on one application, they have a good chance of applying it to another with success.
Brute Force – Taking advantage of the fact that many people use extremely weak, short and straightforward passwords, hackers implement systems to exploit this vulnerability. Often this comes in the form of a ‘dictionary attack.’ when pre-loaded databases of known and potential passwords are stuffed automatically into a website.
Now you know how data breaches involving stolen credentials take place, what they look like and the damage they can inflict, let's take a look at what can be done to prevent them.
10 Password Best Practice Tips
1. Implement MFA - Implement Multi-Factor Authentication (MFA). MFA provides a more robust and secure method when compared to a stand-alone password. Comprised of three different pieces of evidence, something you know, something you have, and something you are, MFA is many times more secure than the traditional password.
Implementing MFA provides an extra layer of protection. Cybersecurity expert David Stubley explains that when you execute MFA "straight away, you are mitigating the most common form of external compromise, brute force attacks because you're not only going to have to guess a user's password, you're going to have to trick them into authorising that access as well."
2. Get a Password Manager – The next best thing you can do is opt for a Password Manager. The overarching problem concerning passwords is the sheer volume you have to remember. It is for this reason, weak easy to remember, similar passwords become the norm.
The solution is to opt for a password manager. It can allow you to store multiple login credentials within a personal vault. When choosing a password manager consider the following. Is it encrypted, you'll want to know if your login credentials are stored in a regular text form or converted to a non-legible format. You’ll want to consider its ability to work across numerous devices and with multiple operating systems. You'll also need to know if you can complete authentication steps automatically or through manual input. Take a look at PC Mags comprehensive list of password managers to choose which best suits your needs.
Quick Tip: Make sure you enable copy and paste features when adding a manager. You'll want to be able to quickly copy and paste the passwords from your vault into the credentials section. Without this function turned on it can become an extremely time-consuming process, especially if your password manager has generated a complex password such as *G8h$#m$dt|I”.
Password managers are handy tools in simplifying the password process. However, they suffer from the same problem as other applications that require passwords; they also need one. You can't get around not having a solid understanding of best practices.
What then goes into the making of a good password.
3. Never Reuse – To drastically reduce the chance of a hacker compromising multiple accounts, deny them the opportunity to reuse a password.
Your password should be unique each time and unrelated in any way to previous passwords. It is also essential to try and eradicate any pattern or systematic approach when creating passwords.
For example, if your Facebook password was Facebook123, a hacker could probably take an educated guess at your twitter password.
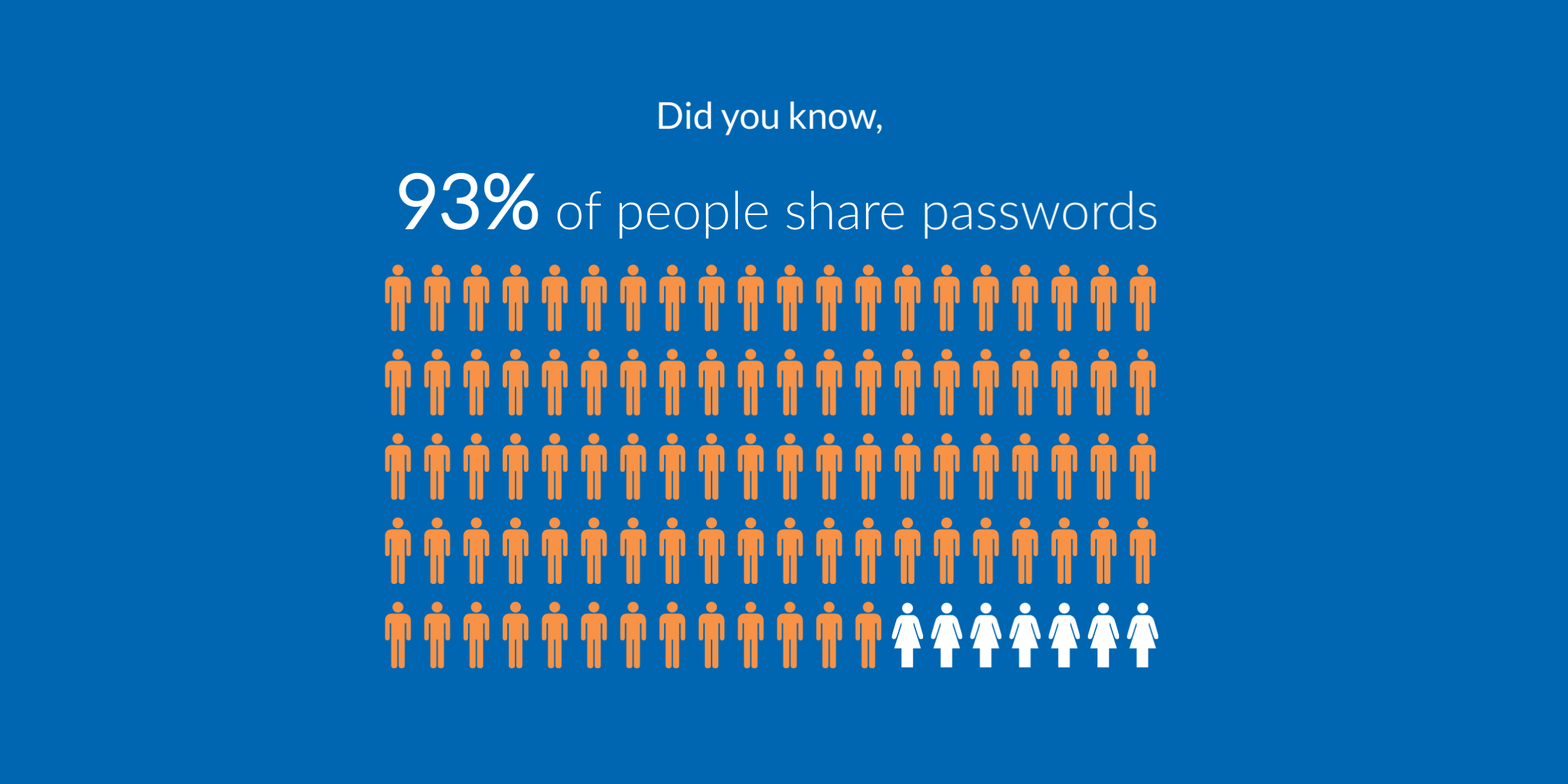
4. Never Share – regardless of how obvious this may seem it is a poorly practised element of password hygiene.
The LastPass 2018 Global Password Security Report found that the average employee shares six passwords.
This statistic is a significant concern for business managers and IT administrators as employees often share weak, memorable passwords in an unsecured manner to remain productive. Today's workers are continuously relying on greater digital applications across numerous devices, and the increase in password sharing is a way to cope with that. However, not only does it constitute poor password hygiene, it exposes the business to a significant risk of backdoor entry by an external actor. As the number of people who use that password grows, so too does the opportunity to exploit it and them.
As a workforce grows, it is essential to track how passwords are proliferating.

5. Passphrases Trump Passwords – This then is the crux of what makes a good password. Ironically it's a passphrase.
The problem with most passwords as noted is that they are often repetitive, short, weak words or sequences with slight variations across applications. Once a pattern is spotted a swath of login credentials can become compromised.
If your password was ‘1234’ it's just as feasible that such little care has gone into other credentials.
This is where passphrases can become extremely useful. Not only are they long and unique, reducing the risk of compromising dictionary attacks, but they can also be incredibly memorable.
For this, you could use a lyric from one of your favourite songs, a line in a movie or quote from a book.
For example ‘welcome to the Hotel California.’ To strengthen it again you could add the year in which it was written or add another identifying factor related to that song. ‘welcome1 to9 the7 Hotel7 Californ!a.’
To bolster its strength include both upper and lower case, add numbers, spaces and symbols as shown.
The main strength of passphrases is that as the amount of characters increases, it becomes exponentially harder to crack for a hacker. With each additional character, it becomes a significant order of magnitude harder to break using brute force methods.
6. Create your Own Blacklist – Just like a hacker uses a database of known and potential password options, so should you. Subscribe to a third party provider of known databases and disqualify any weak passwords (password managers often offer this service).
Use a blacklist in conjunction with inline streaming. This is when you create a password, and it gives you feedback on how strong your password is. This can be a capable system in diminishing a hackers potential to reuse compromised credentials and dictionary attacks.
7. Limit Login Attempts – Limiting the number of login attempts can be a useful tool in stopping a person from randomly guessing a password as well as helping to identify a potential attack.
The immediate benefit of limiting login attempts is in its ability to defuse a potential attack. If a random person tries to access an application by randomly guessing, and fails multiple times, the application can be automatically disabled. Preventing further attempts.
The second benefit of limiting the number of login attempts is in its ability to identify unusual activity and preserve the integrity of your device. If a device or application does become disabled, it is a visible indication that a threat may be present and active. However, merely monitoring password attempts can shed light on unusual behaviour. For example, If an employee is working away on a personal device in a public space, then extra vigilance should be taken. several failed attempts may indicate suspicious activity, warranting an audit.
Quick Tip: correspond login attempts with the user's access to sensitive information or position. For example, an employee who works in marketing with access to non-sensitive material should be afforded numerous attempts. However, a CEO with access to virtually all information should have to meet a much stricter security stance. A single permitted attempt would reflect this.
8. Automated Reset Process – Users forget passwords and exceed login attempt limits. When this happens, a functioning reset system should be in place.
Not only will it relieve the burden on your IT team, but it should also encourage better password practice in general.
People don’t want to be nagging the IT staff for a password reset every week. It's personally embarrassing and is time-consuming. One way people get around this is by implementing and reusing weak personal passwords.
When you automate the reset system and take away the embarrassment of having to deal with an IT administrator, people are more effectively encouraged to implement more complex passwords.
When implementing an automated password reset system, it should consider the following factors.
- It needs to be integrated and straightforward. There needs to be a clearly defined process to recover your password.
- It should contain details regarding who requested the reset, where the reset request originated.
- Notify the user of any time-sensitive reset links and how to request another.
- Contact details for further support.
- Whatever form that reset process takes, it has to look official. Many users are wary of resetting passwords if the correspondence doesn’t match brand image or tone. To them, it may seem like a phishing attack.
- It should never contain the new password.

9. Rotate Passwords – Password rotation refers to the changing of passwords at set time intervals. The benefit this brings is that it reduces the window of opportunity a hacker can exploit. If personal credentials have become compromised but expire shortly, it will hinder their ability to implement an effective attack.
The frequency of rotation can vary, but it should also be set, just like login attempts to reflect the users access to critical information.
However! A critical point with regular rotation is that it is dependent upon users implementing best practice principles. A counter-argument to regular rotation is that it can encourage the recycling of old, weak and simple passwords as users become fatigued with constant resets. Mitigate this by employing a password manager and following best practice principles.
Quick Tip: notify the user in advance that a reset is forthcoming. This can prevent suspicion and allow the user to think up a strong password should they desire to do it themselves.
10. Stop Using Unique Questions – The use of unique questions to recover a password is now insecure. Sometimes you are prompted to provide your mother's maiden name or your date of birth. Well, these are now obsolete given how much personal information is available on social media platforms. What was once private is no longer.
Still using these unique questions can leave you vulnerable as it provides another vector for attack.
Summary
Business leaders and their employees need no longer clash over password practices. By implementing our 10 best practice password tips not only will you ensure you are safe, but productive also.
One need no longer suffer at the expensive of the other.
With the cost of MFA and password managers now more affordable than ever, you can ensure your businesses passwords are as robust and productive as possible.
Configured properly both MFA and password managers can prove to be quicker alternatives to the traditional password, while an automated password reset process can save the valuable time of both users and IT staff.
If you haven't already rushed to your device to implement our best practices, then get to it!
If you have any queries regarding the implementation of these practices then feel free to contact us, we are happy to help!



Leave a Comment