One day, Ali Baba, a poor woodcutter is out hard at work chopping wood in the forest, when he is suddenly distracted. Paying closer attention, he overhears a band of thieves gaining access to a magical cave containing vast treasures. Equipped with the secret password he waits until they depart and makes for the entrance of the magic cave. Once upon it, he merely repeats the words “Open Sesame” and with that enters and makes off with the treasure.
What has this got to do with anything?Well despite the story of Ali Baba being hundreds of years old, and set in a time when electricity hadn't been discovered, it is a perfect analogy as to why you should drop Single-Factor Authentication (SFA) and adopt Multi-Factor Authentication (MFA)!
SFA is when an individual is required to verify their identity through a single category of credential. In the tale of Ali Baba, as it is for the majority of people in real life, that is something we 'know,' or as we more readily recognise, a password!
The major weakness of this approach, however, is the fact it relies on only one type of evidence to verify a users identity.
In this instance, Ali Baba simply had to provide the one type of evidence the cave required, something he knows; the password! Is this not so dissimilar to modern scenarios?
Imagine for a minute you contact your bank and are asked to provide three pieces of evidence all based upon something you ‘know.’ Secret passphrase, date of birth, mothers middle name. If someone nearby is listening in, he or she technically have all the pieces of evidence to take on your identity and pass the security screening.
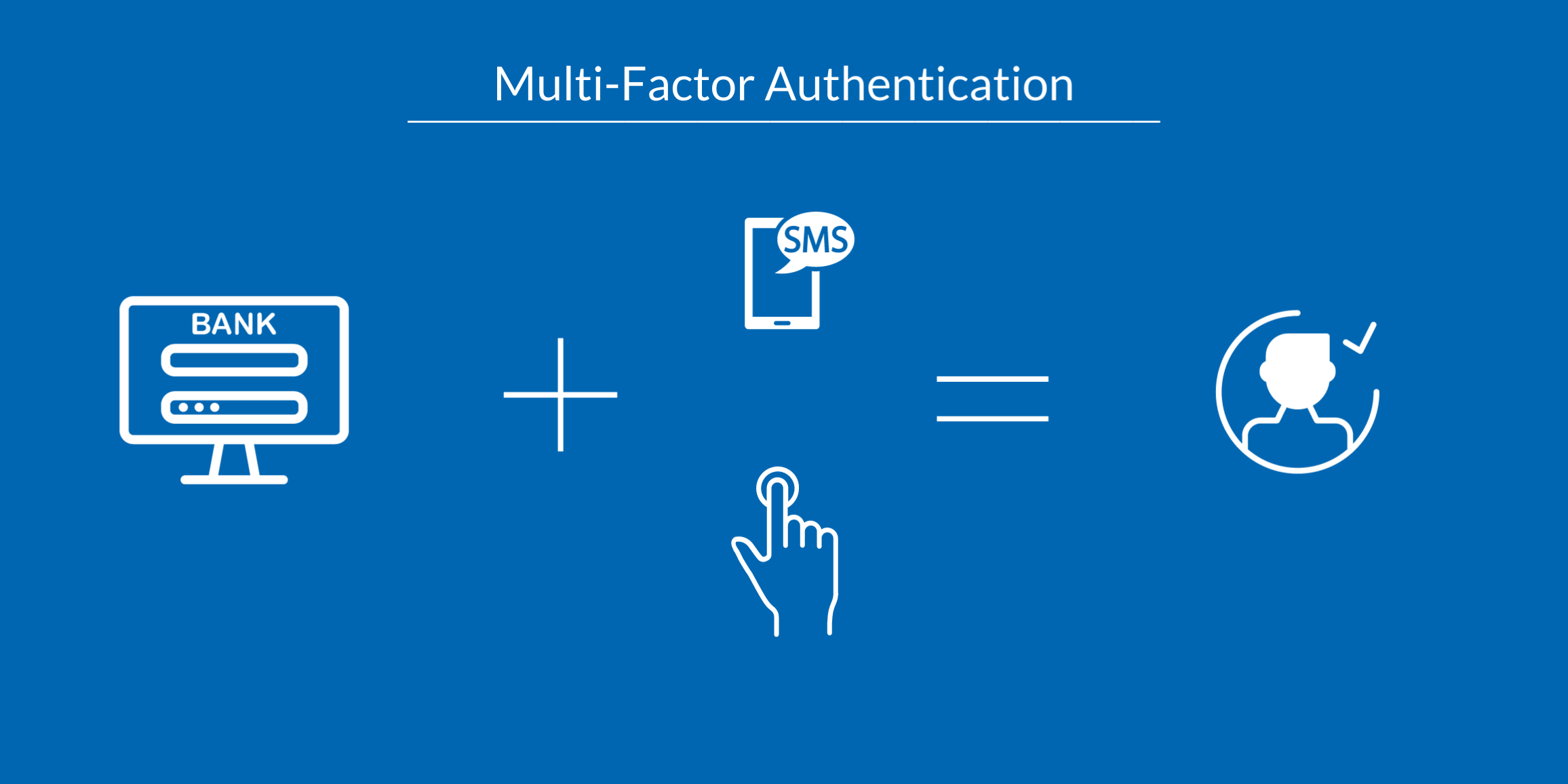
A strategy the cave would have been wise to employ, was MFA. MFA then refers to the method of verifying an individual’s identity by requiring two or more ‘types’ of evidence.
Let’s now examine what contacting your bank might look like using this more secure method. You open up your mobile banking app and try to access your account. First, you will be asked to provide something you ‘know,’ your password. Once you have submitted this, you will then have to provide a second type of evidence. Depending on how your MFA is configured, this could be something you ‘have’ in the form of a one-time password, pushed via SMS. Similarly, it could be something you ‘are’ in the form of bio-metric data, in this case, a fingerprint. Once a secondary type of evidence is provided, you are then granted access.
By requiring different types of evidence, it makes it harder for somebody to gain all the pieces of the puzzle and assume your identity. In the example above, somebody would have to have your password and your phone or fingerprint. This is why MFA is extremely effective in confirming and admitting only the correct individuals and in today's digital age, it is more important than ever before.
The Verizon 2018 Data Breach Investigations Report found that stolen credentials remain the leading factor in data breaches, while 50% of those breaches were carried out by organised criminal groups.
Despite these alarming statistics, most people still ignore password best practices and have poor password hygiene. The LastPass 2018 Global Password Security Report found that workers share on average, six passwords, while 50% use a personal password for enterprise purposes. Eliminating these dangerous habits and replacing them with a robust MFA framework is essential.
So, while the story of Ali Baba and the 40 Thieves is hundreds of years old, it still happens every day. Except, while the thieves in this story may have deserved to have their treasure stolen, the people in today's version certainly do not.
It's vital you ensure your security is fit for the 21st century and adopt MFA today. If you need help implementing MFA, check out our easy guide below. You’ll learn everything you need to know before getting started.



Leave a Comment