Trust is placed in friends and family and earned by those we don’t know. Our communities depend on it and will not arise spontaneously without it. Trust is an integral part of our lives.
Problematic is that in today's hectic business environment, we are often forced to interact at a moment's notice with people we just don’t know. We may be required to admit them access to critical infrastructure that underpins the very foundation of our business.
Even when we know them, do we really know it's them we are interacting with the entire time?
Thankfully there is a practical workaround for this conundrum.
Supplement trust with control! Or more specifically Multi-Factor Authentication (MFA).
Why trust in Single-Factor Authentication is no longer adequate
Single-Factor Authentication (SFA) is when an individual is required to verify their identity through a single category of credential.
Traditionally this category has been something we 'know' or as we more readily recognise, a password. However, passwords carry an inherent number of risks. They can be shared, guessed, cracked, or captured. (Take a look at our 10 Best Practice Password Tips).
Verizon’s Data Breach Investigation revealed 81% of hacking-related breaches leveraged either stolen or weak passwords. Poor password procedure is the soft underbelly of many businesses.
The major weakness of SFA lies in the fact it uses only a single category of credential to verify a user.
For instance, imagine you contact your bank and are asked to provide three pieces of evidence all based upon something you ‘know.’ Secret passphrase, date of birth, mothers middle name. If someone nearby is listening in, he or she technically have all the pieces of evidence to take on your identity and pass the security screening should they choose.
What is needed is numerous categories of evidence, not numerous pieces of the same type of evidence.
This is where MFA comes in.

What is Multi-Factor Authentication and how does it work
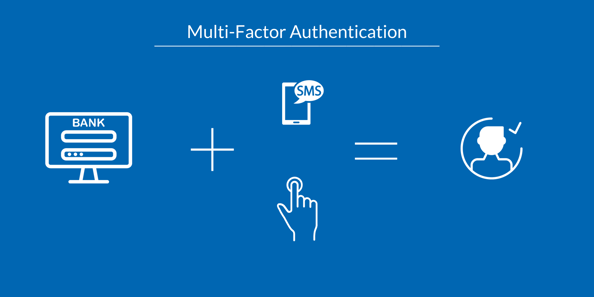
MFA then refers to the method of verifying an individual’s identity by requiring two or more categories or ‘types’ of evidence.
This is seen for example in the form of an ATM; something we ‘know’ in the form of a PIN, but also something we ‘have’ in the form of the physical card. Both are required to access the account.
By requiring different types of evidence, it makes it exponentially harder for a hacker to gain all the pieces of the puzzle and assume your identity. But what are these types of evidence!
The three most predominant types of evidence found in MFA are:
- Something we know (password, PIN)
- Something we have (Phone, card)
- Something we are (fingerprint, voice recognition)
Let's look at a popular configuration of MFA used by many businesses today.
An individual who works for your company is away on a business trip but needs access to your system to continue with work. With MFA you can admit that individual to your system with a very high level of certainty that they are indeed themselves.
The first step is that they provide you with something they know. The person requesting access would submit their password. After this however, a unique one-time password (OTP) will be sent to that individual at the exact moment they require access to your system.
The second step is pushing that OTP to something only they have. This could be a phone or a laptop. Using a OTP, a malicious actor would now need to possess the chosen device as well as the user's password.
In scenarios when this is the case, the third step and type of evidence provides a useful failsafe. The third type of evidence is something you are. Using biometric data such as a fingerprint or facial recognition means that only the owner of the device can access it. The third type of evidence, something you are, thus mitigates the problem of a random person finding and accessing your employee’s device.
Using MFA, access to a system becomes a multi-part puzzle that is exponentially harder to solve for a malicious actor.
Obstacles to MFA adoption
The figures reveal a shift must take place across all industries and within all business when it comes to adopting MFA.
The LastPass 2018 Global Passport Security Report found that:
- While the use of MFA has jumped 24.5% in the last year, only 45% of business in total are using it.
- Businesses considered small (less than 25 employees) had the highest rate of adoption at 41%.
- Businesses between 501 to 1,000 employees had an MFA usage rate of 5%.
- Businesses with 10,001 or more had a measly usage rate of 3%.
Like with any proposed system, concerns arise that impede implementation. With MFA, the hurdles resemble that of most new systems:
- Usability - are employees and clients capable of operating the system efficiently
- Cost – is the system cost effective and good value for money
- Technical gaps and complexity – does the necessary infrastructure exist and in place and how complex is the system to implement
- Backup options – should it temporarily fail, can it be worked around
- Varying risks – are there vulnerabilities within the system
While the concerns surrounding the implementation of MFA are legitimate, knowing what factors to consider can significantly improve successful adoption.
Here’s what you need to consider when adopting MFA.
Factors to consider when selecting an MFA solution
1. User Buy-In - Whether it be employees or clients, you must ensure that users buy into the implementation of MFA. A workforce who rejects a system can frustrate it to the point of failure. To achieve buy-in users need to be educated as to the necessity of MFA for security.
However, MFA has more to offer! Educate users about how MFA is not just another hurdle to productivity but a method to improve it. The added security provided by MFA means you can afford to grant users single sign-on. Once a user is validated through MFA any linked application will grant the user automatic access. This therefore removes the need for numerous passwords for numerous applications. Login fatigue is a significant factor in why people opt for weak rememberable passwords.
2. User Requirements - this relates to the different requirements your users will face regarding their needs, and the adaptability of your MFA system. For example, a worker with concealing facial garments, whether it be for practical or religious reasons should have access to more suitable forms of biometric recognition other than facial. Your system needs to be able to cope with the differing roles and requirements your users place upon it.

3. Adaptive Methodology - This relates to the amount of evidence a user is required to present. It should correspond logically to the types of information the user is seeking to access and the security clearance they hold. For instance, if a member of your marketing team has access only to marketing materials, the MFA process should reflect that. It makes no sense for that individual to present as much evidence and pass as many checks as a CEO who deals with highly sensitive information, on a regular basis. Step-up models can be implemented to require increasing amounts of evidence with increased information sensitivity. If MFA is not to hinder productivity, it must not require more than what is necessary to ensure integrity.
4. Choose Always Available Alternatives -Your system may be required to offer alternatives to phone-based MFA, and it must be considered if the system is to function smoothly. Some users may not have access to reliable mobile reception. If they work underground, for example, it may be more appropriate to have the user utilise a USB with preregistered access codes. A more common occurrence will be users simply forgetting their phones, when this happens an alternative method of access will be required.
Your MFA system has to be able workaround users requiring different access needs.

5. Lost Device Plans - Maybe your employee hasn’t merely forgotten their phone, but have lost it or had it stolen. In this situation, a solid contingency plan must be in place. It may include the following.
- Expire current sessions/suspend access
- Disassociate the device from the user account
- Remote wipe information situated on that device
All these steps would not necessarily need to be implemented instantly in a blanket ban. They can be applied to reflect the scenario. If your employee had lost their laptop in the office, it would not be necessary to wipe all information remotely. It would be however if they lost it indefinitely on holiday.
Once the immediate security concerns have been resolved, attention can turn to providing an alternative method of access for the employee.
6. Think Twice About SMS - OTP is often pushed through to the user in the form of an SMS. While most telecommunication and IT providers implement robust security protocols to safeguard their infrastructure, SMS has been shown to be vulnerable. This can come in the form of a hacker intercepting SMS messages. While this isn't a crisis, it is something to think twice about. Look again to your user requirements and where they operate. Consider this in conjunction with factor 2 and 4.
7. Compliance Standards - Many businesses choose to implement MFA to reach a certain compliance standard. Achieving a certain compliance standard not only ensures your business is proficient within a specific aspect, but it may also be a requirement by an entity you're looking to work with.
Supply chain verification is under the microscope like never before, given the recent high-profile incidents of compromise through third party actors. Aiming and achieving a recognised compliance standard can bring real term benefits to your business. Make sure you understand and document the implementation and workings of your MFA system to comply with any audits.

8. Interoperability - Consider where your current IT infrastructure is now. Can it fully facilitate all MFA functions in a wide range of circumstances? Can this be done immediately, or do you need to invest first before you can support MFA?
9. Plan For Future Needs - Before you implement your MFA system, you should be considering not just current needs, but future needs also. If you are a company expecting to grow in the coming years, it makes sense to invest in a system that can confidently handle a large user base and can deal autonomously with a reset process. This will free up your IT personnel for example. Similarly, while we don’t know, what we don’t know, other people do. Contact experts to address any potential forthcoming opportunities you can exploit before implementing MFA.
Conclusion
MFA is a direct response to the limitations present within SFA, and it's no surprise considering just under half of business owners think their employees use simple or weak passwords. While 84% of IT decision makers at businesses with less than 1,000 employees said they would rather have technology in place than rely on policies to enforce strong passwords.
With cybercrime increasing and evolving each day, it has become imperative for all businesses to increase cybersecurity measures to counter this threat. While Implementing MFA won't absolve your business of its security challenges, it absolves you from relying entirely on trust.
If you have any questions regarding the implementation of MFA then feel free to contact us, we are happy to help!



Leave a Comment